The 3-2-1-1 Backup Rule: Protecting Against 2026 Ransomware
Traditional backups are dead. Modern ransomware actively targets them first. To survive in 2026, your business must adopt the 3-2-1-1 Rule: add Immutability to your data protection strategy. Learn how specialized 'immutable' copies create an unhackable recovery path. 💾🔒🛡️
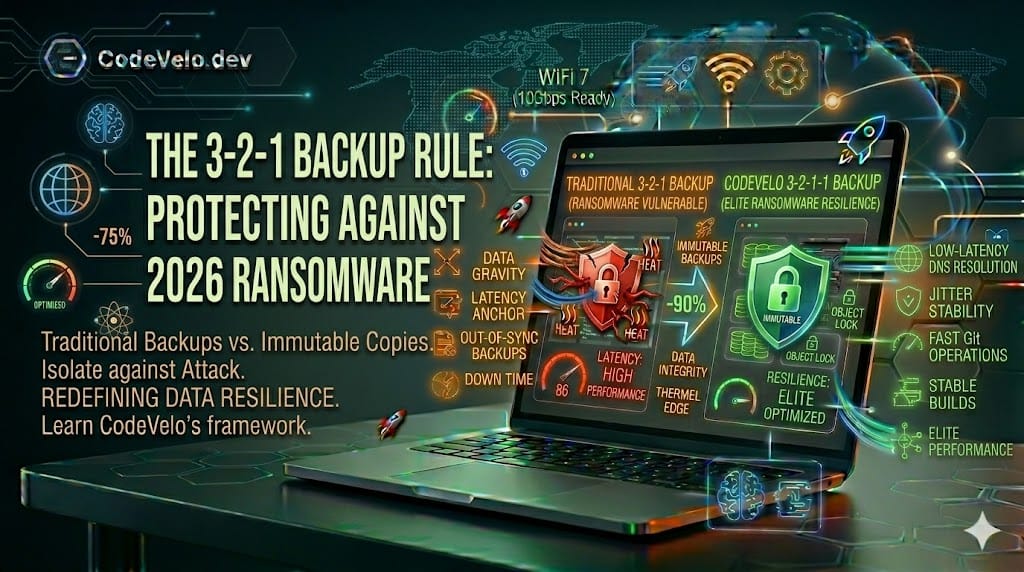
For years, the gold standard of data protection has been the simple "3-2-1" rule: 3 copies of your data, on 2 different media types, with 1 copy offsite. In an era of accidental deletions and hardware failures, this was sufficient. But as we navigate 2026, the threat landscape has changed dramatically. We are no longer just fighting physics; we are fighting malicious intelligence.
At CodeVelo.dev, we've evolved our lessons learned from past data loss. While we are experts in pulling Fiber to the Desk for maximum speed, we treat your data security with the same precision we bring to a Clean Rack Build. To survive the modern ransomware landscape, you must implement the 3-2-1-1 Rule.
1. The Critical Failure of Traditional 3-2-1
Traditional backups, even offsite ones, often have one fatal flaw: they are "hot." This means they are connected to your network. Modern ransomware is smart. Once it breaches your local network (perhaps via a weak VLAN configuration), it doesn't just encrypt your workstations. It moves laterally, mapping your network and actively seeking out backup shares.
If your backup server is connected to the same domain as your primary servers, the ransomware will compromise the backups first. You will only discover the attack when you try to restore your data and find that your secondary and offsite copies are also encrypted or, worse, deleted entirely.
2. The Final '1': Immutability
The crucial evolution of the 3-2-1-1 rule is the final '1': One copy must be immutable.
Immutable backups are data copies that cannot be altered, overwritten, or deleted—even by a root user—for a fixed retention period. This is often achieved using Object Lock technology on storage targets like S3-compatible cloud storage (e.g., AWS S3 Object Lock, Wasabi) or specialized local immutable appliances.
- How it works: When a ransomware attack hits, the malware tries to corrupt your backups. The immutable storage target simply denies the request because the retention policy (e.g., "keep this backup for 30 days") cannot be bypassed. Your core infrastructure may be locked, but your recovery path is secure and mathematically protected.
3. High-Velocity Recovery
An immutable backup is useless if it takes a week to restore. We advocate for a hybrid 3-2-1-1 approach where your immediate recovery target is a high-speed local immutable appliance (connected via 10GbE or better), with a secondary immutable air-gap in the cloud. This aligns your backup strategy with CodeVelo's core philosophy of Performance as a Product Feature—ensuring your business velocity doesn't stop, even during an incident.
The CodeVelo Verdict
In 2026, "I have a backup" is an incomplete statement. You must ask: "Is my backup immutable?" Don't leave your site's velocity vulnerable to a single point of failure.
Is your data truly ransomware-proof? Let CodeVelo audit your backup strategy, implement immutable storage targets, and harden your infrastructure. Secure your recovery path at CodeVelo.dev.